
CEO of major crypto exchange binance Changpeng ‘CZ’ Zhao took to Twitter to warn about the latest hack type targeting the cryptoverse – executed by a “threat actor”. [with] Extensive knowledge of the cryptocurrency industry.”
“Don’t download files!”, Told CZ on Tuesday.
He further explained that users can receive a file from a friend, but that friend may have already been compromised. This person may have shared “a weaponized Excel file” with the name “exchange fee comparison.xls”, which contains a malicious code along with other threats targeting crypto funds.
cz refers to a Microsoft Security Threat Intelligence blog post published this Tuesday, which Discussion “Targeted Attacks Against the Cryptocurrency Industry.”
The blog post states that, given the rise of the crypto market over the past several years, it has attracted the attention of not only investors – but also threat actors who target organizations within the cryptocurrency industry for direct financial gain. We do.
He found that,
“Attacks targeting this market have taken many forms, including the use of spoofing, vulnerability exploitation, rogue applications and information stealers as attackers attempt to get their hands on cryptocurrency funds.”
don’t trust your friends
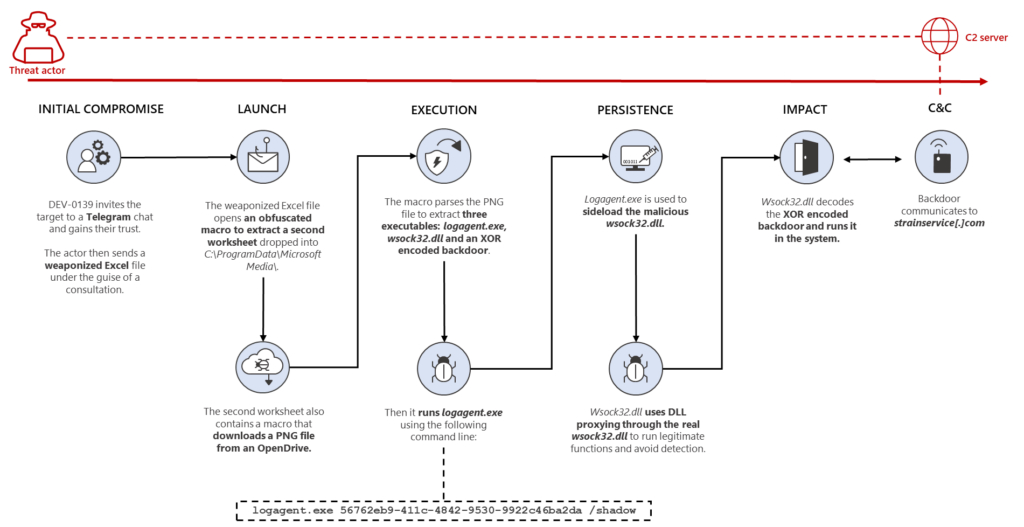
New tactics are also being developed, the report says, one of which was employed by a cure actor tracked as DEV-0139 (the tentative name given to an unknown group of threat activity). as a designation until they are identified and named).
“We are also seeing more complex attacks, in which the threat actor shows great knowledge and preparation, taking steps to gain his target’s trust before deploying the payload,” the report said.
DEV-0139 joined Wire Chat group targeting crypto investment companies. They facilitated communication between VIP customers and crypto exchanges, then identified their targets from among the members.
The threat actor posed as representatives of another crypto investment company, and invited the target to a separate chat group in October 2022, where they pretended to be seeking feedback on the fee structure used by the exchanges.
“The bully actor had extensive knowledge of this specific part of the industry, indicating they were well prepared and aware of the current challenge the companies targeted,” the team said.
However, after gaining the target’s trust, DEV-0139 sent a weaponized excel file containing the names of major exchanges, titled ‘OKX Binance & Huobi VIP fee comparison.xls’, which contained detailed information about fee structures between the exchanges. There were many tables. Specifically, “the data in the document were likely to be accurate in order to increase their credibility.”
attack
The weaponized Excel file initiates a series of activities according to the report. it starts with a macroWhich is an action or a set of actions that can be recorded and executed as many times as needed – when users create macros, mouse clicks and keystrokes are recorded.
In this hack, a malicious macro in the file works to obfuscate some relevant code and recover some data. It will then drop another excel sheet into C:\ProgramData\Microsoft Media\ and execute it in invisible mode. The file then downloads a PNG file that contains three executables: a legitimate Windows file, a malicious version of the executable file, and an encoded backdoor.
All this combined “lets the threat actor remotely access the infected system.”
There is so much more
The report states that the team discovered another file that uses a similar technique, but instead of a malicious Excel file, it is distributed in an MSI (Microsoft Software Installer) package for the Cryptodashboardv2 application. , which is of June 2022.
“This may suggest that other related campaigns are also being run by the same threat actor using the same technology,” it said.
how to defend yourself
The report states that DEV-0139 has “extensive knowledge of the cryptocurrency industry” and that both large and small companies could be targets.
The techniques used by the threat factor can be reduced by adopting the suggested security considerations, he said. While these are instructions for companies, an individual can also use measures to protect themselves:
- Change Excel macro protection settings to control which macros run and under what circumstances the workbook is opened;
- Enable attack surface reduction rules to prevent the common attack techniques seen above;
- Make sure Microsoft Defender Antivirus is up to date and real-time behavior monitoring is enabled;
- use the included compromise indicators to check whether they are present in your environment and assess possible intrusions;
- Educate end users about protecting personal and business information in social media, filtering unwanted communications, identifying lures in spear-phishing emails and watering holes, and reporting reconnaissance efforts and other suspicious activity;
- educate end users about preventing malware infections, such as ignoring or deleting unwanted and unsolicited email or attachments sent through instant messaging applications or social networks;
- Encourage end users to practice good credential hygiene and ensure that Microsoft Defender Firewall is always on.
The crypto industry, be it companies or individuals, has become a common target for various types of attacks. You can learn more about this issue Here,
,
learn more:
, Binance CEO warns users to be vigilant as dark web hackers auction off 500 million WhatsApp numbers
, Binance CEO says they are close to identifying the hacker behind the $570,000,000 exploit
, 25-year-old hacker jailed for stealing $20 million in crypto – find out how he did it
, DeFi Protocol Anker Suffers From Infinity Minting Exploit – Here’s What Happened
Bitcoin Crypto Related Post















